Don’t shoot the #Infosec Messenger
When doing a security disclosure to any organization or company, one must be delicate and careful on how you craft the message to the recipient. [...]
CyberPatriot National Finals this week
This weekend marks the end of CyberPatriot VI with the National Competition at the Gaylord National Convention Center in National Harbor, MD. It has been [...]
2014 Western Regional Collegiate Cyber Defense Competition (WRCCDC) Analysis
Last Saturday marked the beginning of the 2014 Western Regional Collegiate Cyber Defense Competition Season with the successful completion of qualifiers. Over the past four [...]
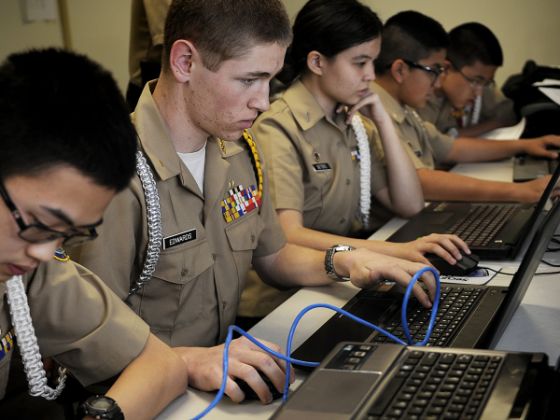
Encouraging Aspiring Future Cyber Defenders
The process of building, nurturing, encouraging, developing, inspiring, and training future cybersecurity professionals is an ongoing lifecycle for us at Net Force. For the second [...]
Perspectives and thoughts on US Cyber Challenge
The US Cyber Challenge is a camp that pushes students to become cyber security professionals. Being a cyber security enthusiast, I wanted to attend. I [...]