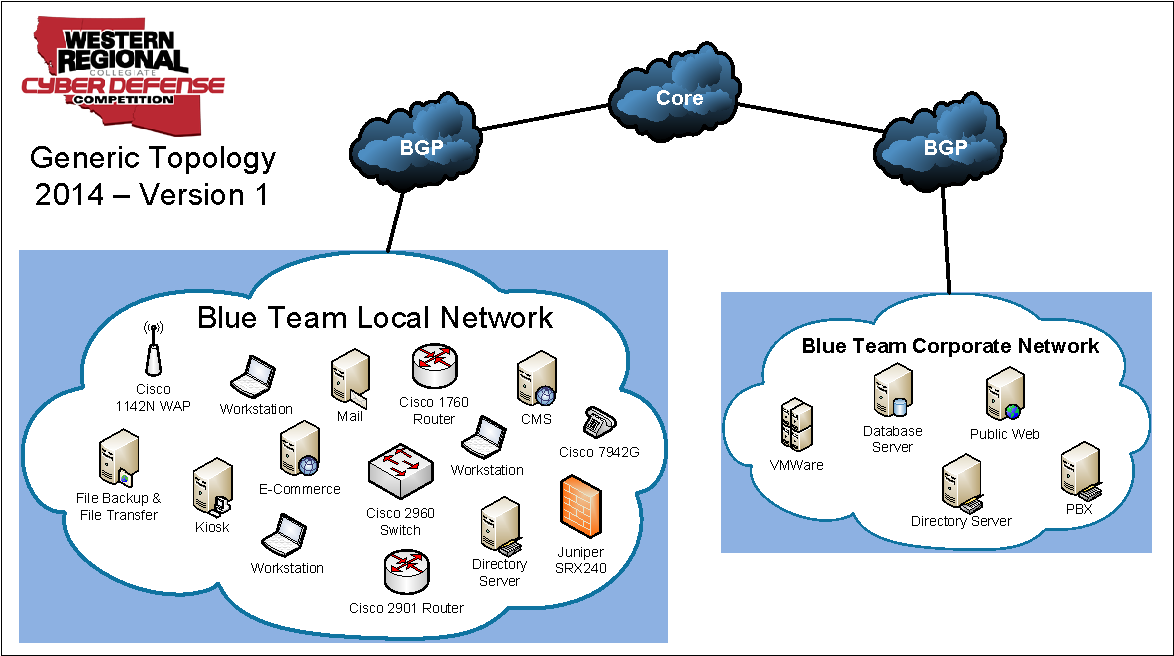
2014 WRCCDC Overview and Debrief
The idea behind CCDC (Collegiate Cyber Defense Competitions) and competitions like it are to allow students to showcase their skills and abilities in a pseudo-real [...]
#AmericanBlackout is really #AmericanFUD
How good (or rather how bad) was National Geographic’s American Blackout? I would argue pretty bad, even if the film was accurate. On Sunday Night, [...]