July 4th 2013 Operations
It may be July 4th weekend for the good guys, but the bad guys are still out there creating trouble. It will be business as [...]
Love, Relationships and Technology – Sharing Passwords
Some considerations while dating. After all, "Revenge" is a dish best served cold.
Report Links Cyber Attacks to China’s Army
If you had not had the chance to read Mandiant's intelligence report on the recent cyber attacks, it's a decent size read that's worthy of [...]
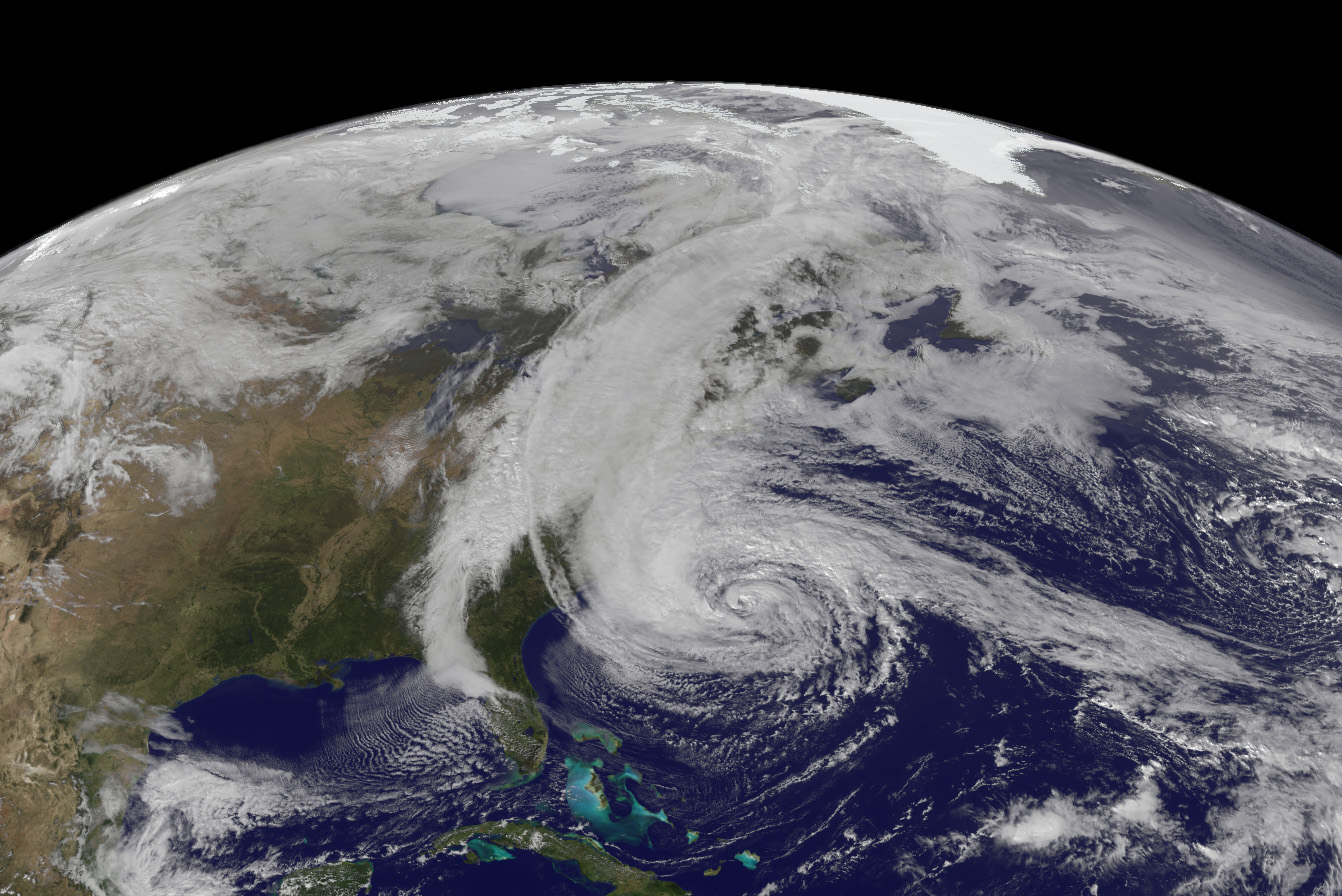
Business Continuity Lessons from Hurricane Sandy
5 Days After Hurricane Sandy... still eerily quiet. Hurricane Sandy, the largest Atlantic hurricane on record, and quite possibly the second most costly [...]
The Secret Social Media Lives of Teenagers
Skirting the rules of not using Facebook.