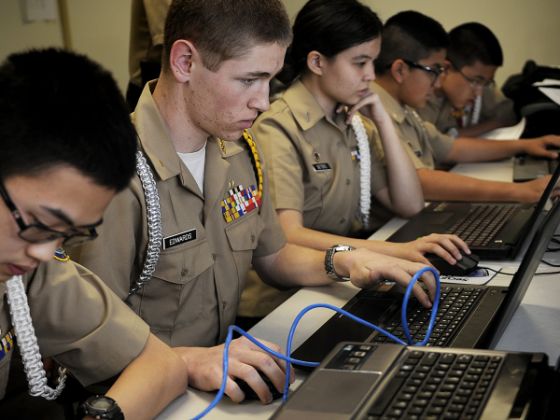
CyberPatriot National Finals this week
This weekend marks the end of CyberPatriot VI with the National Competition at the Gaylord National Convention Center in National Harbor, MD. It has been [...]
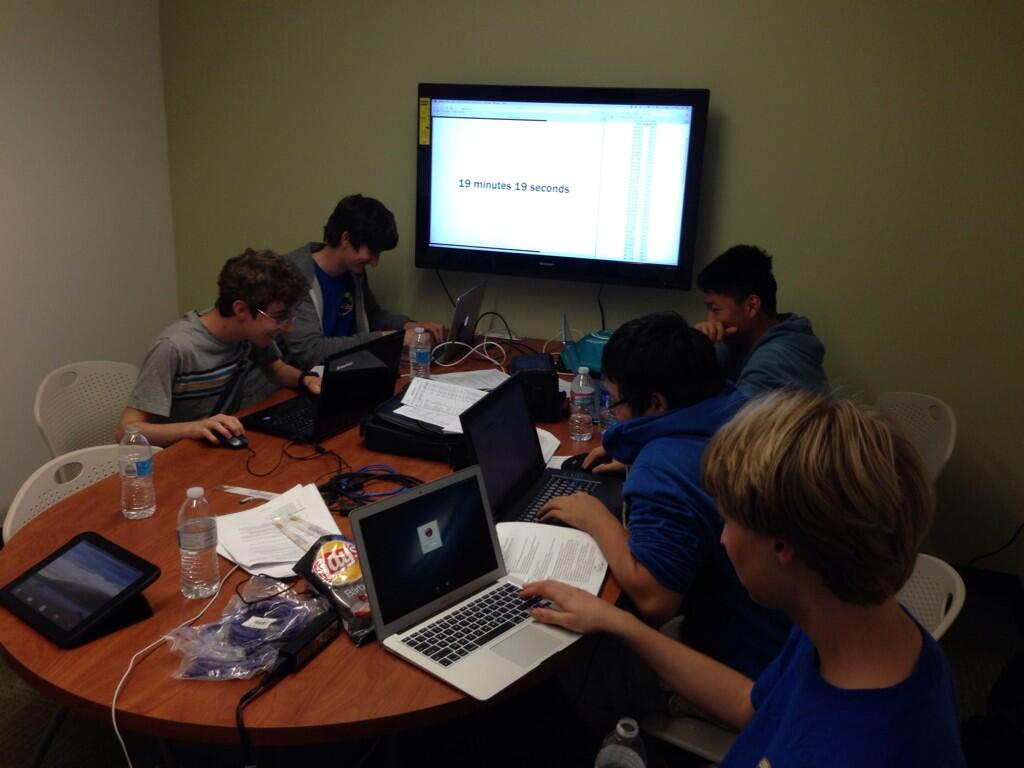
2014 Western Regional Collegiate Cyber Defense Competition (WRCCDC) Analysis
Last Saturday marked the beginning of the 2014 Western Regional Collegiate Cyber Defense Competition Season with the successful completion of qualifiers. Over the past four [...]
4.6 Million SnapChat Username’s and Passwords Leaked
2013 was the year of data breaches, and before the year ended, there was one last data breach. 4.6 million Snapchat customers had their phone [...]
CyberPatriot VI Competition Begins – Round One – GO!
Last weekend officially marked the beginning of the 6th competition season of CyberPatriot. CyberPatriot is a middle and high school cyber defense competition designed to [...]
Fallout Continues on vBulletin Data Breach
As news of the data breach at vBulletin.com and vBulletin.org made mainstream media news, it has left a lot of system administrators and forum administrators extremely [...]